
Course list http://www.c-jump.com/bcc/
Authorization and Preparation.
Identification.
Documentation, Collection (Seizure), and Preservation.
Examination and Analysis.
Reconstruction.
Reporting Results.
Evidence is severely weakened or even suppressed if ECPA/Fourth Amendment privacy laws are violated.
In civil cases, written authorization from attorneys representing organization is needed before gathering digital evidence relating to the investigation within the organization.
A search warrant is needed if evidence has to be seized.
Obtaining a search warrant can be time consuming but is absolutely necessary!
Valid search warrant must particularly describe
the property to be seized and
establish probable cause for seizing the property.
Digital investigators are generally authorized to collect and examine only what is directly pertinent to the investigation, as established by the probable cause in an affidavit.
Sample language for search warrants and affidavits relating to computers is provided in the United States Department of Justice's (USDOJ) search and seizure manual to assist in this process.
For example,
A "computer system" that may have been used to "access" data relating to the production of
financial documents;
computer related documentation, whether in written or data form;
other items related to the storage of financial documents;
records and data for the creation of financial documents;
any passwords used to restrict access to the computer system or data
and any other items related to the production of fraudulent documents;
to seize said items and transport
the computer system,
computer system documentation
and data
to the State Police Computer Crimes and Electronic Evidence Unit for forensic examination and review.
The forensic examination will include making true copies of the data and examining the contents of files.
(Mattei et al. 2000)
Digital investigators are generally authorized to
collect and
examine
only what is directly pertinent to the investigation, as established by the probable cause in an affidavit.
Even in the simple case of a personal computer, digital investigators have been faulted for searches of a hard drive that exceeded the scope of a warrant.
Investigators may seize additional material under the plain view
-- an exception to search warrant requirements.
However, it is not always clear what "plain view" means when dealing with computers...
United States v. Carey, 1998
Mr Carey had been under investigation for possible sale and possession of cocaine.
Controlled buys had been made from him at his residence
Six weeks after the last purchase, police obtained an arrest warrant.
During arrest, officers observed in plain view
a "bong" device for smoking marijuana, and
what appeared to be marijuana in defendant's apartment in plain view.
Alerted by these items, a police officer asked Mr Carey to consent to a search of his apartment.
The officer said he would get a search warrant if Mr Carey refused permission.
After considerable discussion with the officer,
Mr Carey verbally consented to the search, and
later signed a formal written consent at the police station.
Armed with this consent, the officers returned to the apartment that night
Officers discovered quantities of cocaine, marijuana, and hallucinogenic mushrooms.
They also discovered and took two computers
Officers believed computers would either be
the subject to forfeiture, or
the evidence of drug dealing.
Investigators obtained a warrant that authorized them to search the files on the computers for
names
telephone numbers
ledger receipts
addresses
other documentary evidence pertaining to the sale and distribution of controlled substances.
During the examination of the computer investigators found images of CP.
The detective temporarily abandoned search for drug-related evidence and spent 5 hours searching for more CP images.
Mr Carey was eventually charged with one count of CP and sentenced.
In his appeal Mr Carey challenged that CP evidence was inadmissible because it was taken as the result of a general, warrantless search.
The government argued the warrant authorized the detective to search any file on the computer;
Therefore, because any file might have contained information relating to drug crimes, CP came into plain view during this search.
At the same time, the investigator acknowledged
abandoning his authorized search, and
the fact that there was no new warrant before conducting a new search.
The court concluded that the investigators exceeded the scope of the warrant and reversed Carey's conviction --
noting that the Supreme Court has instructed, "the plain view doctrine may not be used to extend a general exploratory search from one object to another until something incriminating at last emerges."
When creating an affidavit for a search warrant, it is recommended to describe how the search will be conducted.
For instance, if hardware is going to be seized, this should be noted and explained why it is necessary to perform an offsite examination.
This is necessary to protect against later criticisms that taking the hardware was unauthorized.
Also, when possible, the affidavit should detail how the digital evidence examination will be performed.
As stated in the USDOJ Manual,
"when the agents have a factual basis for believing that they can locate the evidence using a specific set of techniques, the affidavit should explain the techniques that the agents plan to use to distinguish incriminating documents from commingled documents."
The search leader should prepare a detailed plan for documenting and preserving electronic evidence
The entire search team is briefed carefully how to
protect both the identity and
integrity of all the data.
At the scene, agents must remember to collect traditional types of evidence (e.g. latent fingerprints off the keyboard) before touching anything.
One person should be designated to take charge of all evidence to simplify the chain of custody.
In cases where there is only one chance to collect digital evidence, the process should be practiced beforehand under similar conditions to become comfortable with it.
(USDOJ 1994)

If a computer is to be examined on-site, it will be necessary to know
which operating system the computer is running, and
if there is a network involved.
Usually, a cooperation of someone who is intimately familiar with the computers on site is required to perform on-site search, for example, one of system administrators.
NOTE: in such case system administrators should be included in a pre-search briefing.
The search warrant must specify that the search site should be researched to determine
what computer equipment to expect,
what the systems are used for, and
if a network is involved.
If the computers are used for business purposes or to produce publications, this will influence the authorization and seizure process.
Without all this information, it is difficult to know what expertise and evidence collection tools are required.
First, digital investigators have to recognize the hardware that contains digital information:
computers
floppy disks
network cables, and so on,
Second, digital investigators must be able to distinguish between irrelevant information and the digital data linked to a crime.
Any links between a crime and its victim, or a crime and its perpetrator must be actively sought at the scene.
Printed manuals and boxes related to hardware and software can give hints of what hardware, software, and Internet services might be installed or used.
Before approaching a crime scene, try to determine types of hardware that might be encountered at the scene.
Different equipment and expertise is required when dealing with terabytes of storage versus a miniature system.
Besides desktop computers, consider telephones, hand held devices, laptops, larger server computerss, mainframe computers, network routers, network firewalls, other network devices.
Many forms of storage media include compact and DVD disks, floppy disks, magnetic tapes, high capacity flip/zip/jazz disks, memory sticks, and USB storage devices, such as solid state drives.
Connecting wires and cables are also seized and stored for future examination.
Consider also:
Internet Service Providers that may provide a tour of their facilities for hardware training.
Most system administrators like talking about their networks if asked.
Many computer manufacturers and suppliers have Web sites with detailed pictures and functional specifications of their products.
Different crimes result in different types of digital evidence.
Cyber-stalkers often use e-mail to harass their victims
Computer crackers sometimes inadvertently leave evidence of their activities in log files
Operating systems and computer programs store digital evidence in a variety of places.
Ability to identify evidence depends on investigator's familiarity with
the type of crime,
the operating system (or multiple sytems), and
computer programs that are involved.
Documenting who collected and handled evidence at a given time is required to maintain the chain of custody.
Every individual who handled an important piece of evidence can be examined on the witness stand.
Chain of custody, or continuity of possession, must be established whenever evidence is presented in court as an exhibit.
Investigators involved in the collection and transportation of evidence may be requested to testify in court.
Whenever possible, the chain of custody should be kept to a minimum --
to avoid confusion
to retain complete control of the evidence at all times.
Blank form: chain_of_custody.rtf
Sample entries: chain_of_custody_sample.rtf
A careful note should be made of
when the evidence was collected,
from where,
and by whom.
If evidence is poorly documented, or copied incorrectly, an attorney can easily shed doubt on the abilities of investigators involved in the case and convince the court not to accept the evidence.
If digital evidence is copied onto a floppy diskette or a thumb drive,
MD5 values of the original files should be noted before copy is made.
The target media must include a label with
the current date and time,
the initials of the person who made the copy,
how the copy was made,
the information believed to be contained on the target diskette.
Drive-to-Drive (same machine)
FastBloc
Hardware
Software
Network Crossover (machine-to-machine)
FIM / Enterprise (see next slide)

Multiple corporations with a sense of mutual trust may wish to save costs by
sharing a single application
consolidating data resources
Federated identity management (FIM) is an arrangement that can be made among multiple enterprises.
FIM subscribers use the same identification data to obtain access to the networks of all enterprises in the group.
The use of FIM ia also known as identity federation.
Identity federation offers
economic advantage
convenience
Consider a black box concept of the message digest:
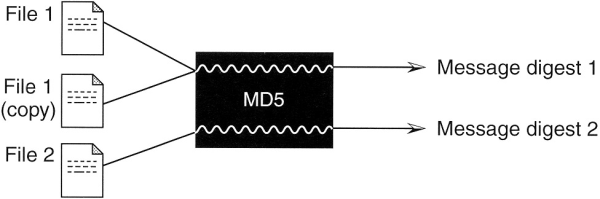
A message digest algorithm can be thought of as a black box that
accepts a digital object -- file, program, or disk, and
produces a number, known as a 128-bit fingerprint.
MD5 example: 5AF576E0EC814482FDF7F12C74BB2D55
Two files that differ by only one letter have a significantly different MD5 values.
The following two examples show two digital inputs and the corresponding MD5 outputs:
"The suspect's name is John" --> C52F34E4A6EF3DCE4A7A4C573122A039
"The suspect's name is Joan" --> C1D99B2B4F67D5836120BA8A16BBD3C9
Since two copies of a digital file are identical, documentation may be the only thing that a digital investigator can use to tell apart the copy and the original.
Inability to clearly demonstrate that one item is the original and the other is a copy badly reflects on the digital investigator.
Similar concerns apply several identical computers with identical components
-- documenting serial numbers and other details is necessary to specifically identify each item.
The computer and surrounding area, including the contents of nearby drawers and shelves, should be photographed and/or videotaped.
At the same time, detailed hand-made sketches and hand-written notes should also be made to facilitate an exact description of the crime scene and evidence as it was found.
When multiple rooms and computers are involved, assigning letters to each location and numbers to each source of digital evidence helps to keep track of all items.
Furthermore, digital investigators may be required to testify years later.
The documentation should provide everything that investigator (or someone else) will need in several years to
understand the evidence, and
ability to verbally reconstruct a crime.
Finally, when examining evidence, keeping detailed notes are required to enable another competent investigator to evaluate or replicate what was done and interpret the data.